Features

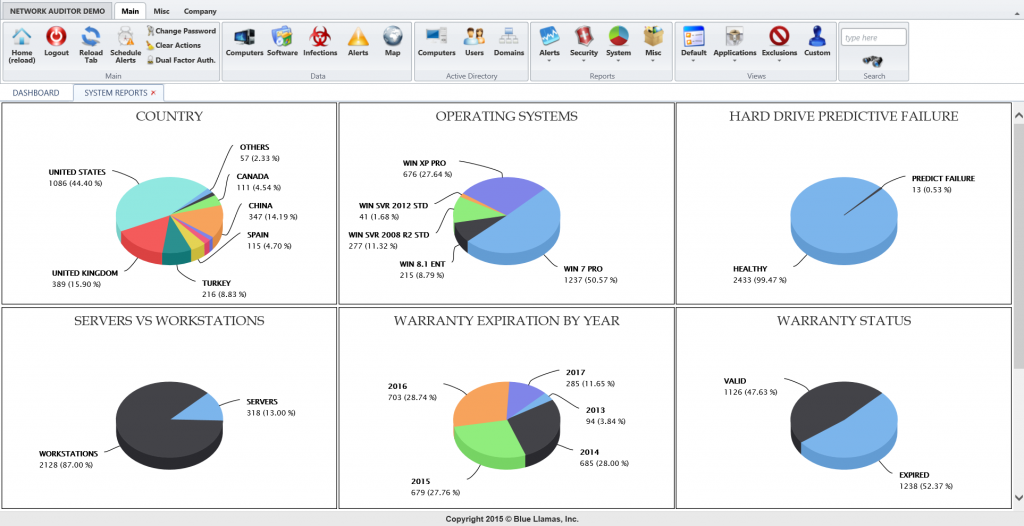
Dashboard Intelligence. It’ll blow your mind.
Look at the big picture. Or the surgical forensic details. From your desktop. Or your tablet in the meeting. Or your phone in the hallway. Know exactly all of the information you need when you need it. And smile knowing that you have the right information in real time.
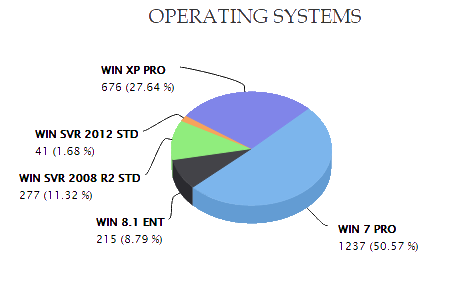
Asset Inventory and Management. See for yourself.
Know everything you have and what state it is in. Right away. Piece of cake. Even manage it remotely. Automate it and get the successful report in the morning. Or on your phone before a good night’s rest.
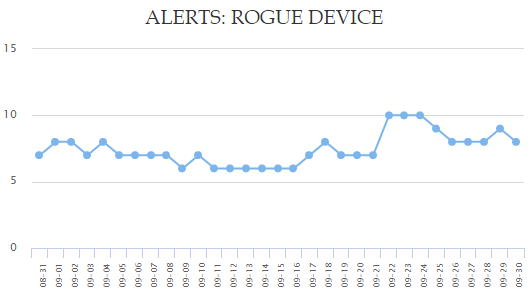
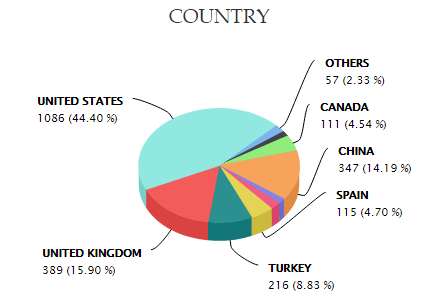
Rogue Device Identification. Checkmate.
Be aware. Know what is connecting to your network. When. And from where. If it doesn’t check out, be alerted instantly. Stop the intrusion and prevent the data loss before it happens.
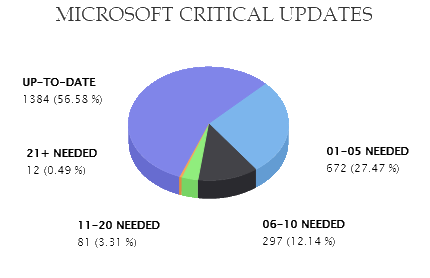
Configuration Management. Peace of mind.
Sleep well knowing that all systems are up-to-date and configured for compliance and safety. Avoid costly and time-consuming intrusion responses due to unpatched systems or pending updates.
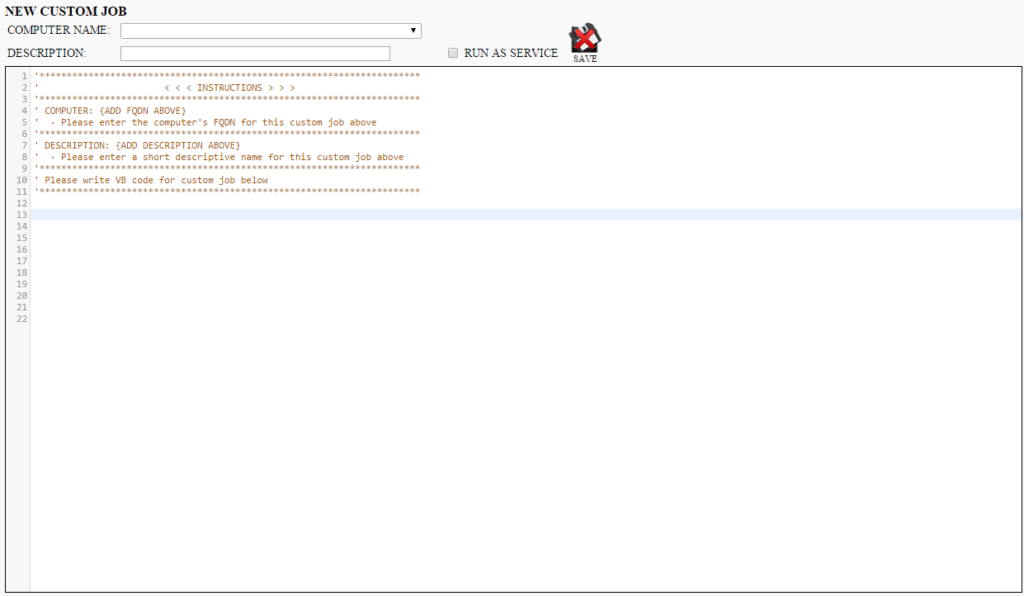
Network Automation. Make it so.
Script anything. Everything. If it can be scripted, it can be done. Now go focus on the important things – like your users’ needs and innovating tech to better support the mission of your organization.
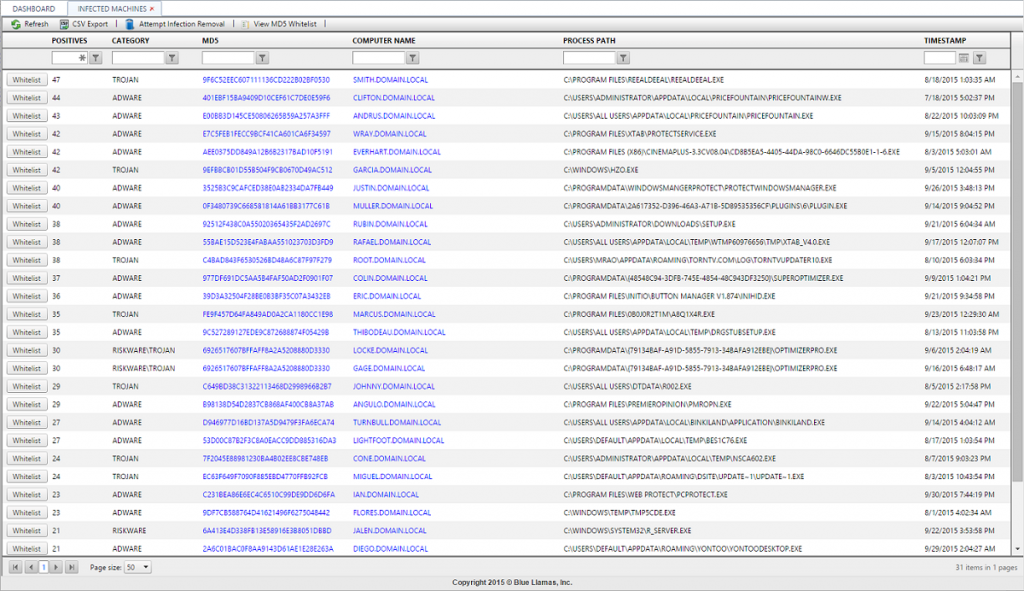
Malware Detection. Every process. On every machine. x 40+ sources.
Are you still betting on just one source to tell you your security has been compromised? Know exactly how infected your environment is right away and which tools will remove the malware your anti-virus software didn’t tell you about.
Asset Retrieval. Lost and then Found.
Have the asset tell you where it is. Log its connections and locations for your retrieval team, security personnel, or law enforcement.
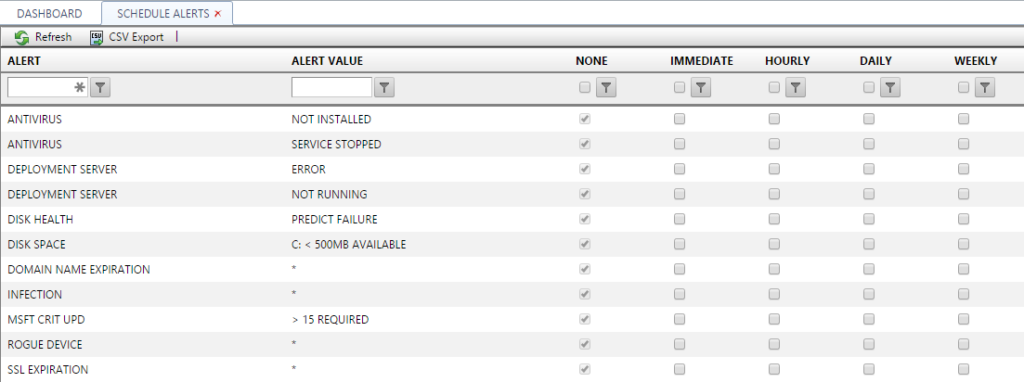
Alerts and Reports. Omniscience.
Know what’s happening when it’s happening. Or before, even. Predicatively. Be notified on any device. About anything. Anywhere. Receive reports you can act on.
